 Top 10 Security Myths
Top 10 Security Myths
Security and protection of Information are a top concern of C-Level executives, yet many still believe these top ten myths. . .
- Organizations are more secure now than they were a year ago
- The presence or absence of regulations greatly matters when it comes to protecting customer data
- External consultants know more about information protection than in-house personnel do
- Information protection must be managed as a separate business unit to be effective
- Complex, frequently changed passwords will make my enterprise secure
- The padlock icon present during an SSL session means my data is safe
- Migrating from Internet Explorer to Firefox or Chrome will make my enterprise secure
- Increased security spending results in greater security
- Wireless networks aren't secure
- Dumping Windows for Linux will increase security
Read on Order Security Manual Template Download sample
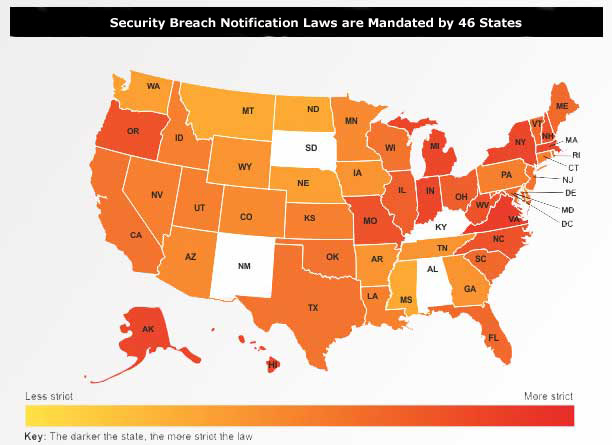
The landscape for CIOs and protection of personal information continues to become more complex as more states add breach notification laws. Currently forty-six�states, the District of Columbia, Guam, Puerto Rico�and the Virgin Islands have enacted legislation requiring�notification of security breaches involving personal information.
Each of these requirements need to be reviewed as the laws typically apply to not only enterprises that have "operations" in those states but also if the state's "residents" or "enterprises" are affected.
Janco's Compliance Management White Paper presents a full list of the states and direct links to the specific law that apply. In addition Janco has update its Security Manual Template and Audit Programs to conform to these requirements.
Order Security Manual Template Download Sample
Compliance Management is CIO Concern
What roles and responsibilities do people have in meeting compliance requirements? What is the impact of BYOD? What are the questions that have not been asked and answered?
Numerous laws and regulatory mandates focus on corporate governance and accountability around sensitive information (specifically financial, non-public information and protected health care information). This has significantly impacted the underlying IT systems that support the applications and repositories holding this sensitive information. Organizations are continuously looking for help in preventing fraud and protecting sensitive information.
The fact that key corporate executives carry personal liability in the event of non-compliance virtually ensures compliance to be a key initiative in any large organizations. Additionally, there are other internal cost-containment requirements that can be effectively met by defining and implementing a sound auditing and compliance methodology. Most corporations agree that compliance leads to better corporate governance and management.
Federal and state government regulations (see state compliance requirements) can be a big problem for today's organizations. There are more than 100 such regulations in the U.S. alone, and that number continues to grow. These are in addition to industry-specific mandates. They are all designed to safeguard the confidentiality, integrity, and availability of electronic data from information security breaches. So, what are the consequences if your organization fails to comply? Heavy fines and legal action. In short, it's serious.
Save over 35%
Special Offer for COBIT Compliance Toolkit
The first step in the process is the creation of an IT Infrastructure that supports best practices processes. These are all addressed in Janco's IT Governance Infrastructure, Strategy, and Charter Template. A further expansion of that infrastructure is supported by the Cobit Compliance Toolkit.
IT Governance Compliance - COBIT Compliance Kit |
Order |
The kit includes:
- Compliance Management White Paper
- Record Management and Destruction Policy Template
- IT Governance Infrastructure, Strategy, and Charter Template
- Disaster Recovery Business Continuity Template
- Practical Guide for IT Outsourcing
- Service Level Agreement Policy Template with Sample Metrics
- Metrics for the Internet, Information Technology, and Service Management
- IT Service Management (ITSM) Service Oriented Architecture (SOA)
- Internet and Information Technology Position Descriptions HandiGuide
- HIPAA Audit Program
- Security Policies and Procedures Template
- Security Audit Program
- Business and IT Impact Questionnaire
- IT Salary Survey
See also CIO IT Infrastructure Policy Bundle
Save over 35% off of the individual product cost by purchasing the COBIT Compliance Toolkit.
Order Compliance Management Kit Download Selected Pages Compliance Kit