Disaster
Recovery & Business Continuity and Security Templates Audit
Bundle
Disaster
Recovery & Business Continuity and Security Templates Audit
Bundle - This bundle is fully compliant with Sarbanes-Oxley, HIPAA, PCI-DSS
and the ISO 28000 and 27000 Series (ISO 27001 and ISO 27002). It has been updated to reflect all of the recent
legislation and other mandated requirements.
The Disaster Planning and Business Continuity Template has been selected by over 2,000 enterprises world-wide as the foundation of their
DRP and BCP programs.
The Security Manual Template has just been updated to
address issues such as SmartPhone and other PDAs
The Security Audit Program contains over 400 unique
tasks divided into 11 areas of audit focus which are then divided into
38 separate task groupings. The audit program is one that either an
external or an internal auditor can use to validate the compliance of
the Information Technology and the enterprise to ISO 27000 (Formerly ISO 17799),Sarbanes-Oxley, HIPAA, and PCI-DSS.
The Disaster Recovery / Business Continuity Audit program identifies control objectives that are meet by the audit program. There are 36 specific items that the audit covers in the 11 page audit program.
Order Security and Disaster Recovery Audit Program
ISO 28000 specifies the requirements for a security management system, including those aspects critical to the security assurance of the supply chain. Security management is linked to many other aspects of business management. Aspects include all activities controlled or influenced by organizations that impact on supply chain security. These other aspects should be considered directly, where and when they have an impact on security management, including transporting goods along the supply chain
The ISO 27000 series is a set of individual standards and documents
defined as follows:
-
ISO 27002 - The ISO 27002 standard is a
renaming of the ISO 17799 standard, which is a code of practice for
information security. It outlines controls and control mechanisms,
which may be implemented subject to the guidance provided within ISO
27001.
-
ISO 27003 - This is a PROPOSED Standard,
which has yet to be completely defined. This will be the official
number of a new standard intended to offer guidance for the
implementation of an ISMS (Information Security Management System). The
purpose of this proposed development is to provide help and guidance in
implementing ISMS. This will be a quality control standard when it is
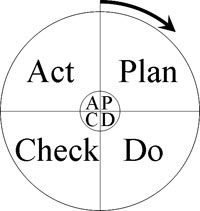
released. ISO 27003 will focus on utilizing the Plan-Do-Act-Check (PDCA)
method, when establishing, implementing, reviewing, and improving the
ISMS.
-
ISO 27004 - This is the designated number
for a PROPOSED standard covering information security, system
management, measurement, and metrics.
-
ISO 27005 - This is the name of a PROPOSED
standard emerging standard covering information security risk
management. As with the other standards within the ISO 27000 series, no
firm dates have been established for its release. However, it will
define the ISMS risk management process, including identification of
assets, threats and vulnerabilities. This is the ISO number assigned
for an emerging standard for information security risk management.
-
ISO 27006 - This standard offers guidelines
for the accreditation of organizations that offer certification and
registration with respect to ISMS.
DRP BCP and Security Audit Bundle contains the following:
 Security Audit Program - Self Scoring Tool
Security Audit Program - Self Scoring Tool
- Comes in MS EXCEL and PDF formats
- Meets ISO 28000, 27001, 27002, Sarbanes-Oxley, PCI-DSS and HIPAA requirements
- Over 400 unique tasks divided into 11 areas of audit focus which are the divided into 39 separate task groupings including BYOD
Over 3,000 enterprises from around the world have chosen at least one of Janco's products. The Security Audit program is a must have tool that not only assists in meeting compliance requirements but also is a great way to validate that your enterprise is ready for your next external audit.
Order Security Security Audit Program
Download Selected Pages
 DR/BC Audit Program
DR/BC Audit Program
- Comes in MS WORD format and PDF
- Meets ISO 27001, 27002, 27031, 28000, Sarbanes-Oxley, PCI-DSS, FIPS-199, and HIPAA requirements
- Includes BYOD and other mobile devices
- Approximately 50 specific items that the audit covers in the 17 page audit program
Order DRP Audit Program Download Selected Pages
Security Manual Template - Standard Edition
- Business and IT Impact Questionnaire
- Threat and Vulnerability Assessment Toolkit
- Security Management Checklist
- Full Detail Policies for
- Blog and Personal Website Policy
- Mobile Device Policy
- Physical and Virtural File Server Policy
- Sensitive Information Policy
- Travel and Off-Site Meeting Policy
- HIPAA Audit Program
- GDPR Compliance Checklist to meet EU Requirements
- California Consumer Privacy Act requirements definition
- Consumer Bill of Rights
- Sarbanes Oxley Section 404 Checklist
- Security Audit Program- fully editable -- Comes in MS EXCEL and PDF formats -- Meets GDPR, ISO 28000, 27001, 27002, Sarbanes-Oxley, PCI-DSS, HIPAA FIPS 199, and NIS SP 800-53 requirements -- Over 400 unique tasks divided into 11 areas of audit focus which are the divided into 38 separate task groupings
- Electronic forms that can be Emailed, completed via a computer or tablet, and stored electronically including: Blog Policy Compliance, BYOD Access and Use, Company Asset Employee Control Log, Email - Employee Acknowledgment, Employee Termination Checklist, FIPS 199 Assessment Electronic Form, Internet Access Request, Internet Use Approval, Internet & Electronic Communication - Employee Acknowledgment, Mobile Device Access and Use Agreement, Employee Security Acknowledgement Release, Preliminary Security Audit Checklist, Risk Assessment, Security Access Application, Security Audit Report, Security Violation Reporting, Sensitive Information Policy Compliance Agreement, Server Registration, and Threat and Vulnerability Assessment
- eReader version of the Security Manual Template
Order Security Manual Template
Download Sample
 Disaster Recovery Business Continuity Standard Edition
Disaster Recovery Business Continuity Standard Edition
Disaster Recovery Business Continuity Template (WORD) - comes with the latest electronic forms and is fully compliant with all mandated US, EU, and ISO requirements.
- Fully editable Disaster Recovery Business Continuit template
- Disaster Recovery Business Continuity Audit Program - Compliant with ISO 27031, ISO 22301, and ISO 28000
- Disaster Recovery Manager Job Description
- Manager Disaster Recovery & Business Continuity Job Description
- Application Inventory and Business Impact Analysis Questionnaire
- Incident Communication Plan and Policy with BEST PRACTICES for
- News Conferences
- Media Relations
- Social Network Checklist
- Included with the template are Electronic Forms which have been designed to lower the cost of maintenance of the plan. Electronic Forms that can be e-mailed, completed via a computer or tablet, and stored electronically including:
- LAN Inventory, Location Contact Numbers, Off-Site Inventory, Personnel Locations, Plan Distribution, Remote Location Contact Information, Server Registration, Team Call List, and Vendor Contact Information
- Added Bonus - Safety Program Electronic Forms -- Area Safety Inspection, Employee Job Hazard Analysis, First Report of Injury, Inspection Checklist - Alternative Locations, Inspection Checklist - Office Locations, New Employee Safety Checklist, Safety Program Contact List, and Training Record
Order DRP BCP Template Download DRP BCP Sample

 Security Audit Program - Self Scoring Tool
Security Audit Program - Self Scoring Tool  DR/BC Audit Program
DR/BC Audit Program