Newsletter Topics
- Compliance Kit Updated
- IT Infrastructure Management - Premium Edition has 22 Electronic Forms
- Security Manual Updated with Electronic Forms
- Core Disaster Recovery Business Continuity Assessment
- CIO and IT Manager Productivity Tools
Compliance Kit Updated
Compliance Program -10 Step program to follow
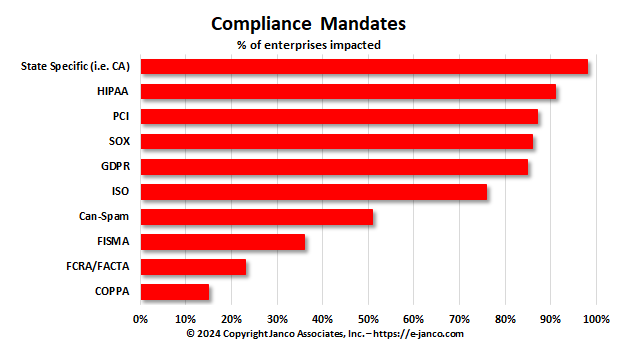
CIOs and CSOs are now under a great deal of scrutiny not only from their executive management but also from a range of governmental and industry regulatory bodies. Janco has created a ten step program that helps them address compliance issues directly. The program, when used in concert with Janco's Compliance Management products gets them in front of the issue.
More small and mid-sized business are impacted by state mandated (i.e. California, Massachusetts, New York, and others) than federal and SEC mandates.
Read On Order Compliance Management Kit Download TOC
IT Infrastructure Management -- Premium Edition Has 22 Electronic Forms
In many enterprises, CIOs are perceived as mere technology managers, while in reality they should beviewed as business leaders. The CIO's focus should be on reducing costs and improving profitability through the strategic usage of IT. It is very important for the Information Technology organization to get out of a transactional mode. If the CIO has the right infrastructure in place, then the CIO can help in directing the strategy of the enterprise, and even shape its destiny. The CIO brings his own perspective, and without IT, you cannot build a robust and business.
The CIO Infrastructure Management Tool Kit is comprised of a collection of Janco products that CIOs and IT Managers can use to create a strategy and manage in the ever changing business environment.
Or you can get the CIO Infrastructure Policy Bundle which includes the following policies with Electronic forms. The policies have just been updated to comply with all mandated requirements and include electronic forms that can be Emailed, filled out completely on the computer, routed and stored electronically. A totally solution that uses technology at its best.
Read on Order Infrastructure Policies Download Sample
With Premium Edition - 22 Electonic Forms:
- Company Asset Employee Control Log
- Disaster Recovery - Business Continuity LAN Node Inventory
- Disaster Recovery - Business Continuity Location Contact Numbers
- Disaster Recovery - Business Continuity Off-Site Inventory
- Disaster Recovery - Business Continuity Personnel Location
- Disaster Recovery - Business Continuity Plan Distribution
- Disaster Recovery - Business Continuity Remote Location Contact Information
- Disaster Recovery - Business Continuity Team Call List
- Disaster Recovery - Business Continuity Vendor List
- Email - Employee Acknowledgement
- Employee Termination Checklist
- Internet & Electronic Communication Employee Acknowledgement
- Internet Access Request
- Internet Use Approval
- Mobile Device Access and Agreement
- New Employee Security Acknowledgement and Release
- Preliminary Security Audit Checklist
- Security Access Application
- Security Audit Report
- Security Violation
- Sensitive Information Policy Compliance Agreement
Read On Order ERP Job Descriptions Get Sample Job Description
Electronic Forms Added to Security Policies and Procedure Template
Version 9.1 of the Security Manual Template has been updated with fourteen electronic forms
J
anco Associates has just released version 9.1 of its popular Security Manual Template. Included with this update are fourteen electronic forms which are needed by any organization that wants to manage its security policies and procedures. The CEO of Janco said, “We have found that it is much easier and less costly to use electronic forms which can be emailed, filled out on a computer or tablet, and filed electronically than using traditional paper forms. “ In addition, “This also paves the way to a very green solution which utilizes technology to reduce the overhead in managing the security requirements of enterprises of all sizes.” He added, “With the ever increasing mandated compliance requirements we have updated this template four times in the last twelve months. We continue to update all of our products to meet both management requests and mandated requirements.”
Forms that can be Emailed, completed via a computer or tablet, and stored electronically including:
- Application & File Server Inventory
- Blog Policy Compliance Agreement
- BYOD Access and Use Agreement
- Company Asset Employee Control Log
- Email � Employee Acknowledgement
- Employee Termination Checklist
- Internet Access Request
- Internet & Electronic Communication Employee Acknowledgement
- Internet Access Request
- Internet Use Approval
- Mobile Device Access and Agreement
- Mobile Device Security and Compliance Checklist
- New Employee Security Acknowledgement and Release
- Outsourcing and Cloud Security Compliance Agreement
- Outsourcing Security Compliance Agreement
- Preliminary Security Audit Checklist
- Privacy Compliance Policy Acceptance Agreement
- Security Access Application
- Security Audit Report
- Security Violation
- Sensitive Information Policy Compliance Agreement
- Social Network Compliance Agreement
- Telecommuting Work Agreement
- Text Messaging Sensitive Information Agreement
- Threat and Vulnerability Assessment
- Work From Home Work Agreement
- Plus more
Core Disaster Recovery Business Continuity Assessment
Many businesses have never tested the recovery process in the event of a server or site failure
With business continuity a core component of risk management, a well-rehearsed plan lays the foundation for confidence that IT systems will work when needed most.
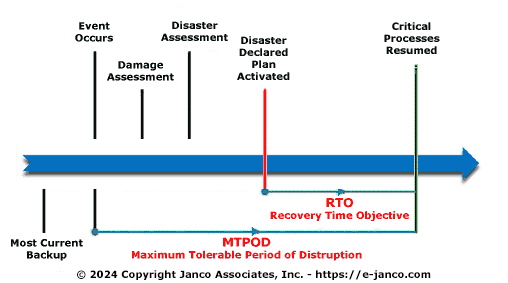
Terms like Maximum Tolerable Period of Disruption (MTPOD), recovery time objective (RTO) and recovery point objective (RPO) are often used, but what do they really mean? In practical terms, recovery time objective is the duration until a business can return to normal after the failure of a server or key computer site, and recovery point objective is the place in the transaction flow where the business resumes.
- Recovery Time Objective (RTO) - How long can your business afford to be down?
- Recovery Point Objective (RPO) - How often do you backup? How much data can your business afford to lose in the event of a disaster?
- Level of Service (LOS) - What are your business' critical servers and essential units that cannot be disrupted?
Implementing a disaster recovery plan includes documenting the process to bring a server or group of servers back online in the event of failure. An overlooked step in the process often flows from the assumption that an IT expert is always readily available. Due to the inherent unpredictability of a disaster, the IT staff that your company relies on may take time to find and start action. Considering this human latency when developing the recovery plan naturally highlights any undesirable complexity in the systems and processes, and the need to support recovery even with minimal IT expertise on hand.
- Core disaster recovery and business assessment questions
- Could a newly hired IT professional quickly handle the situation?
- Could a remote IT engineer talk a novice through the procedures?
- Could a smart phone, tablet, or remote laptop provide all needed access to bring your business back online?
- Could the disaster recovery business continuity plan be executed within the RTO and RPO requirements?
In addition to reviewing your disaster recovery and business continuity plan your team needs to define a realistic picture of their expectations. You could spend too much time thinking of costly alternatives to cover aspects of daily operations that may not be critical. When doing so, ask yourself and your executive team:
- Specifically, what level of protection is necessary (RTO, RPO, LOS)?
- Which aspects of your company's business must stay operational?
All of this is defined in Janco's "Disaster Recovery - Business Continuity Template".