Social Networking Policy Template
Comes with Electronic Social Networking Policy Agreement Form, Electronic Internet and Electronic Communication Agreement, and three full job descriptions
Updated to reflect impact of latest web and security developments. Includes
- Best Practices for Social Networking
- Three full job descriptions: Chief Experience Officer, Manager Social Networking, and Social Media Specialist
 With increased adoption of social networks among the public, organizations have begun setting up profiles within social networks as a means to further connect with their audiences. Organizations who have been most successful in these endeavors take time to survey the community, understand the values and rules of engagement. In short, they pay attention to the culture and identify what is accepted before they join.
With increased adoption of social networks among the public, organizations have begun setting up profiles within social networks as a means to further connect with their audiences. Organizations who have been most successful in these endeavors take time to survey the community, understand the values and rules of engagement. In short, they pay attention to the culture and identify what is accepted before they join.
Organizations that have had success within social networks, remember that this isn't a place for traditional public relations tactics but a place for engagement. These organizations don't always just talk about themselves, but they have real and human-toned conversations with real people.
Order Social Networking Policy Download Selected Pages Version History
Social networking is going corporate. The popular technology used by millions of people to share ideas and photos on MySpace, Facebook, Linkedin and others is catching on at companies to improve productivity and communication among workers. Private, internal social networks make sense as companies grapple with a slumping economy that has made travel cost-prohibitive even as work forces are spread out as never before.
Janco recommends that companies embrace social networking because:
- Social networking is here now- Workers increasingly have Internet access on their smart phones. As of 2022, almost 65% of the worlds population are global mobile Internet users (5.1 billion people worldwide) are accessing social networks from their mobile devices.
- Most employees use it wisely and for the benefit of the enterprise - Some CIOs fear that social networking would lead to "Networking" instead of doing their jobs. Employees with proper training and guidance use this new "technology" in ways that will enhance the enterprise's products an services.
- Social networks actually can make workers more productive - Three out of four of the 895 experts interviewed for the recent Pew Internet report The Future of the Internet IV, said that use of the Internet enhances and augments human intelligence, and two-thirds said use of the Internet has improved reading, writing, and rendering of knowledge.
- Great ideas are gems that are ready to be found on social networks - Great ideas can come from any level of a company. Using social networks internally (wikis, blogs, forums, even IM) fosters collaboration, and allows workers at all levels to contribute ideas.
- Employees are trustworthy - Managers worry that employees will leak confidential information, or speak poorly of the company. but with the proper training and procedures in place this is a non-issue.
The issue faced by enterprises of all sizes is ensuring that the right message is being communicated in a consistent manner. The first step in achieving this objective is to have a uniform social network policy.
The Social Networking Policy Template is the right tool for this task. With it you can successfully manage and control your employees' activity that are related to your enterprise.
Order Social Networking Policy Download Selected Pages
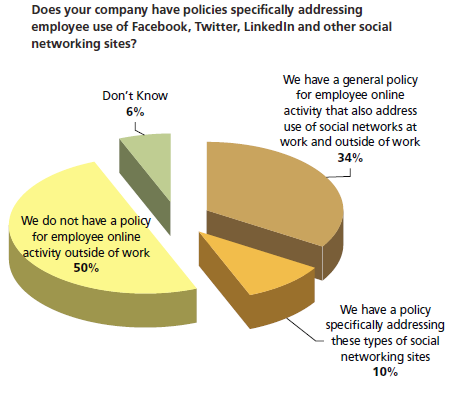
Social and business networking sites are changing the way people talk on-line. Sites like Facebook, MySpace and others help friends stay in touch while Linkedin mainly connects business users. They are very popular but present new challenges to IT managers.
These sites are continuing to proliferate. Facebook is the second most popular site in the world and is continuing to grow in popularity with nearly 60% of global Internet users visiting the site in December of last year.
- The numbers of users on the site in 2012 exceeds 3.2 billion, 90% of which were located outside of the US.
- The rapid growth in popularity and usage of such sites is just part of the problem.
Companies unaware of the associated dangers of these types of websites risk getting caught of guard.
Risks Include:
- Inadvertent disclosure of confidential information is also a risk. You wouldn't publish your
organization chart and phone directory on the Internet; but a head-hunter or identity thief can use information on social networking sites to reconstruct this kind of information. - Sites that allow third parties to run applications that have access to user profiles. This is a potential privacy risk. People publish a wealth of personal information in their profiles. This makes social networking sites a happy hunting ground for identity thieves and con men.
- Social networking sites can be addictive and time-consuming. Cyber-slacking is a genuine
concern. - There is also a risk to your company's reputation. Social networking is more public and less formal than company e-mail. It is also easier to use than blog software. It's easy to imagine employees posting pictures or text that would embarrass their employer.
- Viruses and spyware: Social Networking sites often display advertisements.